44CON 2023: It takes a Village
- 7 minutes read - 1348 wordsAs I stare at my laptop after an intense few days at 44CON, I reflect on the experience. I went through a lot of different emotions. Excitement, trepidation, relief, bewilderment, pride, disappointment and hope had accompanied my visit to London to 44CON. We had an OSINT Capture The Flag competition happen right next to a round-table discussion on how the government should secure the country. Looking from outside in, a rallying cry of “Hack the Planet” (if you want to feel old, it turned 28 during the con) side-by-side with the establishment might not be the first thing to expect at a security conference.
Excitement
My first indication of the great things that were about to come was just chatting away with Carl and Alfie, who were at the conference to get into security. For me that was a really nice sign of things to come. Infosec is not a closed shop that gatekeeps people out, we can’t be hiding behind certifications and degrees. I first met them in the lift and had a chat with them as we were waiting for people to arrive. Little did they know that I usually feel socially awkward and quite introverted.
On the other end of the experience scale, I got chatting to Yiannis who had over 20 years of security experience, worked in government and was CISO for a bank. It was my turn to feel like an impostor and get excited, I chatted to him about my talk and - shock - I didn’t feel completely out of place.
The excitement only built when the evening keynote kicked off. Jen told us about her career, building a bridge between government and infosec, and shouting out some of the important work done in the community to help out. It is no good complaining about regulations if we don’t try to make them. Wow, she’s done some cool shit.

Trepidation
When I first saw the Track 1 room, I gulped. This room was far bigger than any talks I’d done before. I’d be on a stage, there’s expensive lights and chairs. A lot of chairs.
Fortunately Adrian, who introduced himself to by saying “Hi, this is my con”, was on hand to build up my confidence, telling my about how he was impressed by the perspective that my CFP brought and that I shouldn’t worry. It was really impressive, putting me instantly at ease and I did not feel like that this was the first time I met him. After the slick video and laser open show, the virus-killing cool-blue pillars to keep Covid at bay and the specialist coffee, it should not surprise me that he knows just what I needed.
Lovely! And because of the bright lights I couldn’t see anyone in the audience anyway!
Relief
My talk went well. I was a little bit disappointed not to get any questions, but I guess I had been chattering away about the topic enough.
On day two of the conference, we had a great talk by Paul, who told us what it was like to be portrayed by Simon Pegg in the “Undeclared War” and about the other 99% of boring stuff that didn’t make it into the filming. You know, the challenges brought on by supporting Ukraine, how to deal with Russia, Iran, North Korea, China and keeping a whole country safe.

Talking of North Korea, Nick presented a fascinating OSINT insight into the DPRK, which has the sum total of 30 web servers, and they tend to be quite flaky, so knocking North Korea off the internet is not as impressive as it sounds.

Wait, You Promised a Village
It was Jen who wasn’t finished yet. She was running the Policy Village which brought people from the UK government who weren’t “here to help” but “here to listen”. What was it that would make the country more secure? What would security researchers, hackers, CISOs, pentesters, blue and red teamers want. As it happened it was a big table with lots of interesting opinions and I found it fascinating talking with people who write the policy in the cabinet office, different departments or the NCSC. I suppose I fitted in. Doing AppSec at HMRC is part of the puzzle.
My rookie move: asking someone who works at the NCSC for a LinkedIn connect.

Bewilderment
Now, at previous conferences I had focussed on talks, this time I wanted to explore some of the workshops. Kevin’s Kubernetes workshop was really quite interesting. K8s is a massively powerful, super complex, and that brings lots of opportunities to shoot yourself in the foot and provide attackers an in. It was interesting to attempt a CTF and try to find clues, but my lack of K8s showed. And I’d never done a CTF either. But for a few hours, I loved hacking away, scrolling through kube man pages and cursing the computer. I still think that Kubernetes is too powerful for its own good, but it was fascinating to look.
More bewilderment was to follow at the night session, when James from Project Zero talked about his 8-year Odyssey to get Microsoft to fix a bug class properly, illustrating how much more expensive (for Microsoft) a quick fix is than understanding the root cause of a problem. A whole heap of vulnerabilities could have been prevented if they had been interested in fixing more than the Proof of Concept. If putting a sticking plaster on an arterial bleed sounds familiar, don’t worry, you’re not on your own…
I particularly liked the slide illustrating the black hole of Redmond
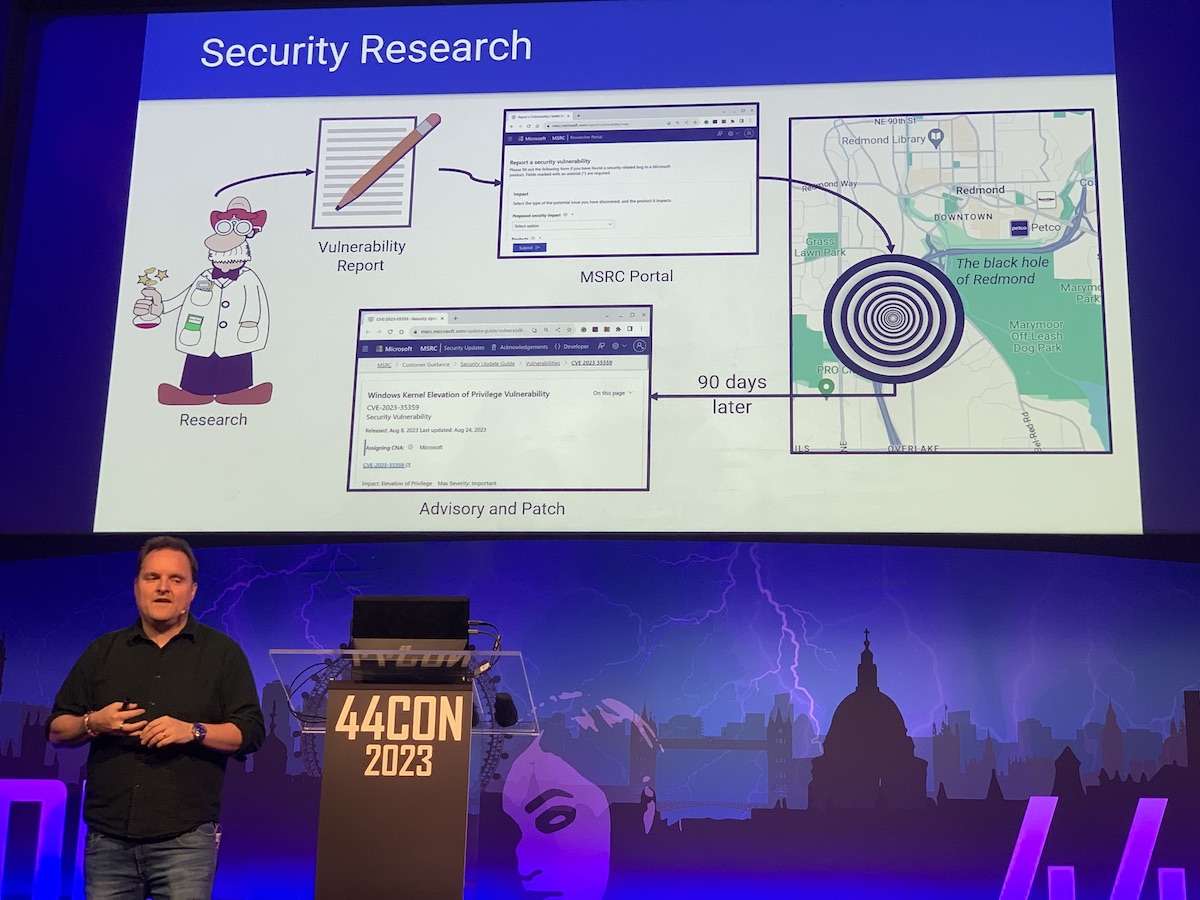
In the interests of balance, there’s a black hole of Cupertino too, and my guess is that in Mountain View products are just cancelled way before any long-running bugs can be found.
Pride
To close the conference, Phil explained to us what it means to secure the NHS. He worked on securing the Test & Trace programme, at a never-before seen scale, pace and purpose. I found it quite inspirational the way he talked about the fact that trusting people and getting them to “do first, check later” was the only way of getting things done. The stories about how people just hunkered down and worked themselves close to hospital to improve things for patients was quite something. I felt a similar energy when it came to playing a small part delivering the HMRC response at scale and pace.

Subsequently, he took the small challenge of securing the whole Health and Care sector, which means all the way from hospitals to your neighbourhood pharmacy. About 140,000 organisations, representing 12% of the GDP of the country.
Disappointment?
Well, obviously I was gutted when it had finished!
Hope
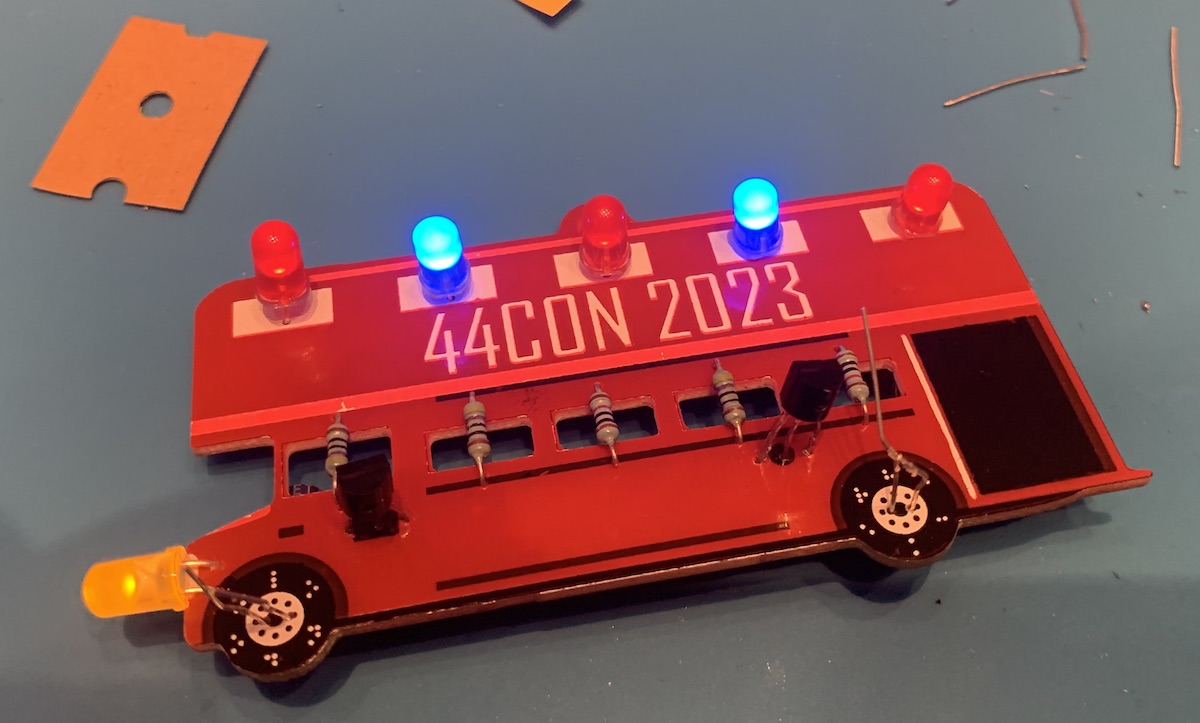
I hope that has given you a flavour about what it was to be at 44CON. Definitely worth a visit, I didn’t even mention that I picked some locks at 11:30 at night and was soldering transistors, LEDs and capacitors on my badge and it even worked!
One last thing, I loved all the conversations, hope that LinkedIn will allow me to stay in touch with some really interesting people and continue some great conversations. Probably one of my favourite ones was on the tube on the way to the station after it finished. I got chatting about how I think that AppSec just does not work if security is not closely working with developers. Shift left is on everyone’s buzzword bingo card, but I think it is what needs to happen. As development gets more agile and continuous, so must security. A yearly pen-test tick box security theatre exercise is not enough. Blocking deployment for 2 weeks while waiting for a CAB is no longer working. The pandemic has shown us what is possible, I think we need something like the Agile Manifesto for making change. Come to think of it, the agile manifesto isn’t a bad starting point. “We value people over process”. Well, no shit, if there’s one thing the conference taught me, it takes collaboration! Let’s make sure the developer and security community gets closer together.
If you'd like to find more of my writing, why not follow me on Bluesky or Mastodon?