BSides Leeds 2023: Get the basics right
- 3 minutes read - 636 wordsIt is a couple of weeks after my trip to Leeds to go speak at BSides. Now, if you’ve never been to a BSides - and I had only been to one prior - then hopefully this gives you a bit of a feel as to what to expect. In short, there’s lots of interesting people with great talks and insights and something that feels just right. A bit of community and some weird people. Weird in a very good way!
Now, I have to admit, that at the beginning I was a little bit put off by all this puff-piecery on how important this spirit of community was and how BSides can be considered family. Note my slightly skeptical body posture:

But by the end of the day, I was very much a convert and already wondering how I would broach the subject of going away for more conferences with my long-suffering wife.
Tell us about the talks
There were many highlights during the keynotes and talks of the red, blue and purple tracks and I tried to go to as many as I could, but a couple of patterns emerged:
Get the Basics Right
Security is not about the latest zero-day or a complicated kill chain linking together 6 vulnerabilities. Of course, these are the things that sound sexy or allow you to register domain names for a cool sounding threat moniker, but more often than not an unsecured network share with a list of passports by applicants will bear more fruit than the latest l33t sk1llz.

It is not also about going straight to a red team supplier and getting them to physically break into your office and hack into the printer while wearing black pyjamas. That’s no use if you have not even had a pen test. Or you had a pen test but haven’t implemented the recommendations.
Getting the basics right is the first advice from red, blue and purple teams. I’m still a tad unclear as to what
the exact differences are, just that the red keynote ribbed the blue team, the blue team speaker made fun of purple
and the purple keynote was more profane that anything. Profane is not a typo. #youhadtobethere

Experimental
One of my favourite speakers on the day was James Bore who took his talk down a very fundamental rabbit hole, making us question what is meant by “a business”, what is meant by “security” and “safety”. Illustrating once more that getting the basics right and even questioning the language that we’re using make such a big difference.
I was reminded of Ian Levy changing the abbreviation of “APT” from Advanced Persistent Threat to Adequate Pernicious Toe-rag. It changes the threat landscape a little bit if instead of throwing money at vendors to save us from Matrix-style uberhackers that will pwn us no matter what, we think a little bit about the risks.
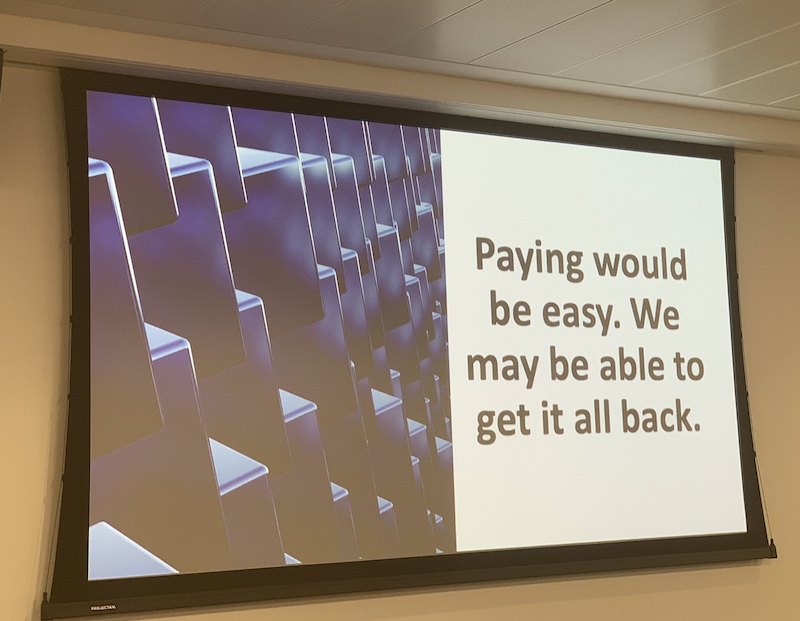
Talking of money, I very much enjoyed Lisa Forte’s demotivational posters about how to deal with ransomware
Was it all talk?
Well, it was a shame that the programme was so packed. I did manage to pop my head into the InfoSec Battle Bots and pick up a couple of stickers at the sponsor stalls. But I didn’t get to do the lockpicking or car hacking or the scavenger hunt (though that might have been a good thing, judging by the fact that when I sat in the green room I was most amused by a conversation about whether shaving eyebrows off could be eligible for scavenger hunt points or not - like I said, weird but in a good way).
I thoroughly enjoyed the day. Oh and I did a talk based on this post too. Which was fun!
Thank you BSides Leeds. Community rocks! Go if you have the chance!
Tags bsides conference securityIf you'd like to find more of my writing, why not follow me on Bluesky or Mastodon?